Started the month by dipping back into Mechs vs. Minions. We’re on to mission 5. We lost almost immediately and then restarted for another try. After an extended slog we successfully pushed the bomb onto each of the repair pads.
On my birthday I took the day off of work and we spent the afternoon starting Tales from the Red Dragon Inn (which I got for my birthday last year; too many games to play, too little time; though I was waiting for a 2nd-edition update kit which got released in the interim). We played scenario 1.1 and successfully defended the inn from the out-of-control training automata. It’s a fairly simple dungeon-crawling game with a campy atmosphere. So the emphasis is on fun rather than deep tactical analysis. I appreciate that the characters give a complexity rating to enable effective selection by family members of varying skill levels.
A couple days later we played scenario 1.2 and were victorious in fighting our way through the inn’s cellar to the intrusion site and defeating the giant gelatinous blob.
At the board game meetup I played a couple of ecological games. First was Undergrove in which you manage supplies of nitrogen, potassium, phosphorous, and carbon to grow mushrooms in the shared forest and then grow trees within the forest to enable end-game points.
It’s a clever game inspired by real growth networks of fungi. However, a design issue in which accuracy harms playability is that you manage both potassium and phosphorous and the tokens are denoted by chemical symbol. So potassium, is ‘K’ and phosphorous is ‘P’. Really easy to reach for the ‘P’ when you’re looking for potassium if you’re not already comfortable with potassium being ‘K’ (as occurred regularly by players in my game).
Overall I enjoyed the game, though I did not win. Lots of variety and opportunities for varying strategies, however it did seem like some locations were substantially more beneficial than others. Maybe there are strategies to balance that which I couldn’t see in a single play through.
The second ecological game of the night was Petrichor. It’s a game of clouds, rain, and crops. You add clouds to the grid of crops, move those clouds around, increase the water in them, and try to strategically rain on the crops. Each round you get a hand of cards which determine which actions you can take.
Whenever I learn a new game at an event my focus is on understanding the rules well enough to make valid moves on my turn that are not obviously bad and keep the game moving. Sometimes I “get” a game and can try to apply intentional strategies after a couple of turns. This was not one of those games. My moves were intended only to be shallowly useful to me based on the objectives I was able to easily understand with no grand strategy behind them. But sometimes that’s enough and I won this game. I think it’s much more strategically challenging than the fairly simple table presence would suggest.
A friend hosted a game day which I was able to stop by at for a few hours. Started by playing Explorers of Navoria. Each player has an expedition team on each of 3 continents. Nominally your task is to explore these continents and settle villages, however it turns out you can more or less ignore that aspect entirely and earn plenty of points doing other things. So from that perspective I think the designers missed something. I won, but I also felt like I didn’t play the game the way it was intended. There’s a too-powerful shortcut to points by focusing on a single tribe and grabbing a couple of cards that gives you points for each person in the tribe (which is what I did).
Explorers of Navoria was a little bit longer of a game and most of us were looking for something light and short to play next. That turned out to be Animals Gathering.
In Animals Gathering you are a mage gathering magical stones to restore lost animals from extinction. What that looks like in practice is rolling dice with shapes on the faces, those shapes determine which tangrams you can pick up and use to fill in the tangram-silhouettes of the animals on the cards you collect. But any shapes from your roll that you can’t use your opponents get to use. The dice have different shape distributions and you get to choose which dice you’ll roll. So there’s a little bit of strategy and tactics involved, but overall it’s light and easy to play. I won this but, if I recall correctly, the points were something like 26, 25, 25, 24. So extremely close.
After Animals Gathering we were waiting for another group to finish their game so we played a few rounds of Stool Pigeon. That went: loss, loss, loss, win. At no point did the person who “called” the round end up winning. Which makes sense given the mechanics of the game and makes me wonder about use a reverse psychology approach to the game–“calling” the round with a poor hand on the expectation that people will swap your cards out assuming they’re better than they are. Could be interesting to try.
Jess and I took an overnight trip to the coast for our anniversary and I gave her A Gentle Rain as an anniversary gift. We had both seen it online somewhere and thought she’d like it. It’s a calm, contemplative, solitaire game (you can play in groups by just taking turns). The theme of this game is that the lilies on the lake only bloom in the rain. Today a gentle rain is falling and your task is to lay out the lake tiles to create places where the eight lilies can bloom. There is no winning or losing though you can calculate a score for how well you did if you want. The point of the game is to be relaxing, quiet, and meditative. We played a few times. I don’t remember how many lilies we were able to place in any of the games though. Jess has been able to place all eight a few times playing solo.
At another board game meetup I was able to play a few games starting with Faraway, which I’ve played before. I got trounced in this game. I was unable to realize the main gambit I aimed for to boost my score, so I was quite thoroughly in last place. Still an interesting game in that it’s kind of upside-down engine building. You can only score points on a card based on the cards you play later.
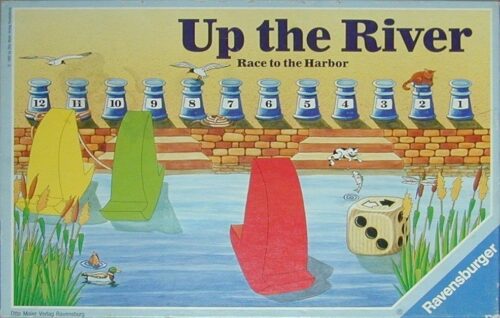
Someone dug up an old kids game from 1988 called Up the River (which was apparently published under several names with the same mechanics and different themes–BoardGameGeek groups them together under the name Race Through Space). It is a deceptively simple game though. You each have three boats and the goal is to sail them to the harbor. The harbor has twelve docks numbered 1 to 12 (which are points) with each boat reaching the harbor claiming the highest available dock. At the end of each round the river flows downstream and if you have a boat at the bottom of the river it’s lost forever. On your turn you roll a die and decide which of your boats to move that amount.
Initially we all tried to save all three of our boats, but by the end we had all lost one. We suspect the better strategy is to strategically abandon one to begin with as gaining docks, say, 12 and 9 will handily win over someone straggling along all 3 boats claiming docks 7, 5, and 3.
Afterwards I was planning to head home, but someone wanted to play Shamans which they said was fairly short. So I let them convince me to join in. It was not particularly short however.
Shamans is a hidden role / defector game, but what I liked about it is that it’s played over several rounds and the defectors are random each round. So getting caught early on doesn’t eliminate you or make it impossible to do anything effective. Bluffing games are not generally my cup of tea–I like to play the games not the people at the table, but this was the most enjoyable one I’ve played because of that resetting that occurs each round removing some of the pressure. I was a defector for 2 of the 3 rounds in the game. I got caught once. The game is a little odd in that you have loyalists and defectors, but it’s still an individual that wins. So you’re operating in an environment of nominal cooperation of all players, but some players are cooperating against the others and everyone is trying to figure out who the teams are each round while also trying to position themselves to earn victory points. I did not win.
Jess and I played a game of Wyrmspan. I won with my strategy of prioritizing the Guild track. Neither of us managed to fill our caves with dragons this time.
And to finish off the month we played Creature Comforts as a family. Jess’ family of squirrels made the coziest home and won.